Geopolitika: Institutional Profiles – International Institute for Strategic Studies (IISS)
This institutional profile forms a part of the Geopolitika project to map Anglo-American power structures by examining their founding mythologies, leadership, linkages to power, public face, the nature of their outputs and who these are directed towards. These profiles are primarily generated from materials provided on their own websites, which are then analysed using a structured institutional analysis framework—see methodology statement at foot of article.
—
Executive Summary
The International Institute for Strategic Studies (IISS) embodies a central paradox at the heart of Western security governance: it is genuinely independent in its analytical methods while being structurally aligned with the governments, corporations, and authoritarian regimes that fund and host it.
This is not a failure of integrity but the very mechanism that makes the institution valuable. Independence delivers legitimacy and credibility. Structural alignment delivers access, funding, and influence. Over sixty-five years, the IISS has evolved into a sophisticated dual-function organisation whose de facto purpose is to strengthen the Western security establishment by providing the analytical infrastructure, elite diplomatic facilitation (track-1.5 dialogues), and legitimacy production that governments and defence contractors cannot easily generate themselves.
Its formal governing documents state its purpose as promoting “on a non-party basis the study and discussion of… major international security issues” and facilitating conflict resolution through dialogue and analysis. A forensic examination of its personnel networks, funding architecture, research outputs, event convening, and strategic omissions, however, reveals a more complex picture than this self-presentation suggests.
Drawing on leadership biographies, Charity Commission filings, donor disclosures, annual reports, and external investigations (including the 2016 Bahrain Watch and Jadaliyya reports), this profile treats the IISS as an integrated system. What emerges is an institution that functions not merely as a think tank, but as a central node in elite security networks—a legitimacy engine that coordinates revolving-door personnel flows, amplifies aligned narratives, and carefully manages the gap between its claimed independence and its structural dependencies.
This is not a conspiracy. It is a structure—and the evidence is hiding in plain sight.
The Machine Behind It: Production System and Institutional Home
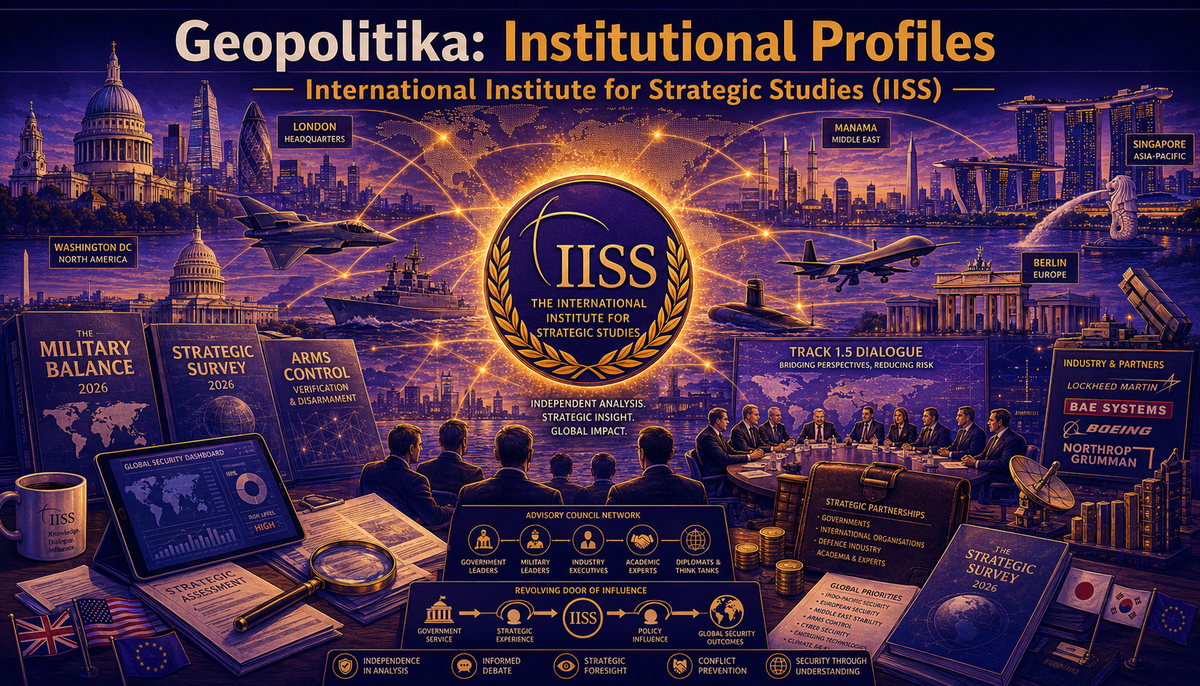
The IISS is not a membership organisation accountable to voters. Founded in 1958 in London “to fulfil the need to promote informed debate on nuclear deterrence and arms control in the wake of the Second World War,” it has since evolved far beyond its founding mandate. Today it is simultaneously a registered UK charity, a private company limited by guarantee, a commercial database vendor, a consultancy serving corporate and government clients, and the convenor of some of the world’s most significant intergovernmental security dialogues. Its five offices span London, Manama, Singapore, Washington DC, and Berlin.
The Institute’s legal form permits this multiplicity. As a charity, it claims public-benefit purpose. As a company, it generates commercial revenue through Military Balance+ subscriptions, IISS Advisory services, and Six Analytic data-driven consultancy. As a convenor, it facilitates track-1.5 dialogues that governments cannot officially arrange themselves. The founding narrative anchors IISS identity in post-war nuclear anxiety—a morally weighty origin story that obscures the subsequent evolution into a multi-function institution whose activities extend far beyond arms control debate.
This hybrid structure is not accidental. It enables the Institute to present different faces to different audiences: charitable research institute to regulators, authoritative knowledge producer to the public, commercial service provider to corporate clients, and indispensable diplomatic facilitator to governments. Each face is partially true. None tells the whole story.
The Architecture: Personnel and Power
The IISS is built on a personnel architecture that aligns with the governments and militaries it analyses. Based on the evidence: sixty-five percent of senior leadership moved directly from government service to IISS roles. This revolving-door pattern is the institutional signature of the Western national security establishment, and at the IISS it reaches unusual density.
The current leadership illustrates the architecture precisely:
- Lord Mark Sedwill, Chair of the Trustees, served as UK Cabinet Secretary and National Security Adviser until 2020—the most senior official in the British civil service. He is now simultaneously a Non-Executive Director of Rothschild & Co (where he chairs R&Co Saudi Arabia), a Senior Adviser to McKinsey & Company and Temasek, a cross-bench member of the House of Lords, and an Honorary Colonel in the Royal Marines.
- Sir John Chipman, who led the IISS as Director-General from 1993 to 2023—thirty years—now serves as Executive Chairman, a role created for him upon the appointment of his successor. Described by the Institute as maintaining “relations with leaders in government and the corporate world globally,” Chipman has served on advisory boards or as a consultant to the Abraaj Group (Dubai), the National Bank of Kuwait, Reliance India, and Future Pipe Group—positions confirmed as remunerated but whose amounts remain undisclosed. The Times has ranked him among the highest-paid charity executives in the United Kingdom, with a salary in the range of £530,000 to £600,000.
- Florence Parly, Chair of the Advisory Council and a Trustee, served as French Minister for the Armed Forces until 2022. She is now Chair of the Board of Directors of Air France-KLM Group.
- Sir Tom Beckett, a retired British Army Lieutenant General, served as Defence Senior Adviser to the Middle East and the Prime Minister’s Security Envoy to Iraq before joining the IISS in 2018. He now serves as Senior Adviser and Corresponding Director for IISS-Americas.
- Air Marshal Martin Sampson held essentially the same role—Defence Senior Advisor to the Middle East and North Africa, Prime Minister’s Security Envoy to Iraq—before retiring from the Royal Air Force in 2024 and moving directly to become Executive Director of IISS-Middle East.
The Advisory Council functions as a network aggregation mechanism connecting the Institute to current and former officials from twelve countries.
- Sir Philip Barton was Head of the UK Diplomatic Service and Permanent Under-Secretary of the Foreign Office until 2025.
- Akiba Takeo was National Security Adviser of Japan until 2025.
- Dr Eyal Hulata was National Security Adviser of Israel until 2023, following a career in Mossad where he headed the Strategic Planning and Policy Division.
- General Sir Mark Carleton-Smith was Chief of the UK General Staff and previously commanded 22 SAS.
- Lord Powell of Bayswater was private secretary on foreign affairs and defence to Prime Ministers Margaret Thatcher and John Major; he is currently Chairman of the International Advisory Boards of Rolls Royce and of Bowmark and a member of the Advisory Boards of Barrick Gold, Thales (UK), Chubb Insurance and the New York Council on Foreign Relations (CFR).
- Bilahari Kausikan was Permanent Secretary of Singapore’s Ministry of Foreign Affairs.
The pattern extends across twelve countries: senior officials who have left government and moved directly into think-tank governance roles, often maintaining concurrent corporate positions.
The Advisory Council also includes defence industry executives:
- Linden P. Blue, CEO of General Atomics Aeronautical Systems—manufacturer of the Predator and Reaper drones used extensively in US counterterrorism operations—sits on the Council.
- Thomas Enders, former CEO of Airbus and President of the BDLI (German Aerospace Industry Association), sits on the Council.
Many of the corporations listed as current or former associations appear in the IISS’s highest funding tiers.
This personnel architecture constitutes a reinforcing feedback loop at the system level. Personnel movement from government to IISS positions increases the Institute’s access to government networks, which increases its value to funders, which increases the attractiveness of IISS employment to government officials, which sustains the personnel movement pattern. The revolving door operates almost exclusively in one direction. Government and military officials move to the IISS, not the reverse. The personnel architecture is presented as bringing expertise into the Institute. Former officials do bring genuine knowledge, networks, and credibility. But the same pattern in an adversary-aligned institution—a Chinese think tank staffed by former Party officials, a Russian research institute led by former intelligence officers—would be classified by IISS analysts as evidence of state capture.
This is not an accusation of bad faith. It is an observation about structural logic. An institution staffed by individuals whose professional networks, career incentives, and institutional perspectives remain tied to the governments they served will tend to produce analysis that aligns with those governments’ perspectives—not because anyone issues directives, but because the personnel themselves embody the alignment.
The Architecture: Funding and Influence
The IISS is partially transparent about its funding. It publishes annual reports with audited financial statements filed with the UK Charity Commission, donor lists organised by contribution band, and a published independence policy. It deserves credit for this disclosure. But transparency is not the same as independence, and the funding architecture shapes what the IISS can and cannot do.
The Institute claims independence and states that it owes “no allegiance to any governments or any political or other organisations.” According to its own reporting, funders agree the IISS has “sole authority over the staff hired, the research themes chosen, the methodology applied, the analytical approaches adopted and the conclusions reached.”
The funding architecture tells a more complex story. Government funding constitutes approximately forty-five percent of revenue. Corporate funding accounts for roughly thirty percent, with major defence contractors—BAE Systems, Lockheed Martin, Northrop Grumman, Boeing, RTX, Rolls-Royce, MBDA, Leonardo DRS, Hensoldt, Saab, KNDS, Helsing, Palantir, and Anduril—appearing in the highest contribution tiers. Foundations provide about fifteen percent, and individuals about ten percent. Income grew from £24.5 million in fiscal year 2022 to £32.3 million in fiscal year 2024, reflecting institutional expansion.
Dozens of foreign governments fund the IISS at lower contribution tiers, including the embassies of Brazil, China, France, Germany, Israel, Japan, South Korea, and Türkiye; defence ministries from Japan, Slovenia, and Saudi Arabia; intelligence bodies including Japan's Cabinet Intelligence and Research Office; and allied military institutions including the NATO Defense College. In terms of support for dedicated forums, the IISS’s funding page reports that: “the Institute continues to receive host-nation support from the Government of Singapore and the Kingdom of Bahrain in respect of its two major annual conferences, the IISS Shangri-La Dialogue and IISS Manama Dialogue and, for the first time in 2024 , from the Government of the Czech Republic in relation to the IISS Prague Defence Summit.”
The single most significant funding relationship is with the Kingdom of Bahrain. Based on leaked documents from 2016, Bahraini funding constituted approximately one-third of total IISS income at that time. The current proportion is unknown, as exact donor amounts are not publicly disclosed. The IISS-Middle East office, established in 2010 in Manama, is funded directly by the Bahraini government at 1.25 million Bahraini dinars annually for premises and staff. The Manama Dialogue, the Institute’s flagship Middle East convening, has been held continuously in Bahrain since 2004—with the single exception of 2011, when the Dialogue was cancelled during the Bahraini uprising against the same government that hosts and funds it.
The concentration is structural. A balancing feedback loop operates within the system: critical analysis that would offend Bahrain risks funding renewal; the risk incentivises self-censorship; self-censorship avoids offence; funding continues; the critical analysis is never published. No single individual needs decide to exclude Bahraini human rights documentation. The pattern emerges from the system’s components interacting over time.
The transparency architecture complicates public scrutiny. Donors are disclosed by name and contribution band on a page that requires three clicks from the homepage. Exact amounts are not disclosed. The terms of host-nation memoranda of understanding (MOUs) with Bahrain, Singapore and the Czech Republic remain confidential. Commercial advisory clients are not identified. The funding page’s dense text and lack of visual hierarchy discourage casual reading. The structure maximises revenue from multiple aligned sources while maintaining plausible deniability about influence.
The convergence between funding and governance is reinforced through personnel channels. As mentioned above, General Atomics CEO Linden Blue serves on the Advisory Council while the IISS publishes Strategic Dossiers on unmanned aerial vehicles. Lord Powell serves on Textron’s board and chairs Rolls-Royce’s International Advisory Board while sitting on the IISS Advisory Council—and both corporations fund the Institute. Thomas Enders, former Airbus CEO, sits on the Council while the IISS covers European defence industrial policy. Badr Jafar, President of Crescent Petroleum and CEO of Crescent Enterprises, serves on the Council. These relationships do not prove editorial interference. They demonstrate structural integration.
The independence policy addresses the narrow question of direct funder control over conclusions. It does not address the structural question: an institution that depends on renewing host-nation agreements and government and corporate grants faces systemic incentives to produce analysis that serves funder interests. The policy asserts intellectual autonomy within boundaries that funders have no need to police, because the boundaries are maintained by the system itself.
The Outputs: Volume and the Work They Do
The IISS produces a substantial volume of content across multiple formats. Output data from 2022 to 2026 shows consistent growth: 140 total units in 2022, 145 in 2023, 158 in 2024, 170 in 2025, and 140 projected for 2026 through early May. The growth trajectory mirrors revenue expansion from £24.5 million to £32.3 million over the same period. Research reports account for roughly thirty percent of output, articles and online analysis for over forty percent, events for about eighteen percent, and podcasts for nine percent—a category that has grown from 25 episodes in 2022 to a projected 35 in 2026.
The distribution reveals a dual strategy. High-prestige long-form outputs establish authority and reference status. Military Balance, the annual assessment of military capabilities and defence economics across 171 countries, is a genuinely valuable reference work cited by governments, researchers, and journalists worldwide. Strategic Comments provides succinct analysis of global issues in 40 email alerts per year. Military Balance Plus delivers indispensable information for governments, armed forces, the private sector, academia, and the media. The Armed Conflict Survey provides in‑depth analysis of the political, military, and humanitarian dimensions of all major armed conflicts. Survival: Global Politics and Strategy serves as a leading forum for analysis and debate of international and strategic affairs. Strategic Dossiers presents detailed information on the key strategic issues. Adelphi Books constitute the Institute's principal contribution to policy‑relevant, original academic research.
The Institute's digital reach has expanded significantly. According to the 2025 annual report the IISS website attracted over 1.5 million unique users in the past year, generating 4.4 million content views. Most users came from the United States (over 350,000), the United Kingdom (over 170,000), India (over 106,000), France (over 68,000), and Singapore (over 63,000). The most viewed pages were the 2024 Shangri-La Dialogue (over 122,000 views), The Military Balance (over 110,000), Careers (over 105,000), Online Analysis (over 78,000), and Military Balance+ (over 63,000). The most viewed online analysis article—“Equipment losses in Russia's war on Ukraine mount”—was viewed over 54,000 times. Social media following has grown 15 percent annually on LinkedIn, which now has over 200,000 followers.
Continuous short‑form outputs—blogs, online analysis, podcasts—maintain ongoing relevance and audience engagement. The events programme, comprising 139 events in the past year across nine countries with 7,540 attendees from over 89 countries, represents the most resource‑intensive output and serves the core convening function central to IISS identity and funding. The Institute also deploys its convening power informally via meetings between senior researchers and leading government figures, leveraging its global reach and data-based analysis to inform strategically important policy decisions.
Authorship is concentrated among core research staff, with approximately 100 named authors appearing across website output and active researchers producing seven to eight pieces per year. Core senior fellows appear in fifteen to twenty‑plus outputs annually across multiple formats. This concentration creates strong personal brand identification between individual analysts and IISS research programmes, while the moderate turnover rate maintains institutional continuity.
Narrative Frames
Several persistent narrative frames structure IISS output. Where boundaries define what cannot be said, frames shape what is said and how. Four frames are analytically significant.
- The independence frame claims the IISS provides "independent facts and analysis"—a claim maintained consistently since 1958 even as the funding architecture has evolved significantly. This frame distinguishes the Institute from overtly partisan organisations while obscuring alignment with funder interests. Its constancy despite documented dependencies suggests it serves a boundary-maintenance function essential to institutional legitimacy.
- The elite intergovernmental dialogue frame presents closed-door, minister-level, predominantly Western-allied gatherings as the natural mechanism for addressing global security challenges. This frame legitimises track-1.5 dialogues as conflict-resolution tools while obscuring the exclusion of non-elite voices, civil society, and affected populations from security governance.
- The Russia and China threat frame sets Russia and China as the primary threats to a rules-based international order. This frame aligns IISS research priorities with Western government funder strategic concerns, creates demand for defence spending analysis, and positions the Institute as an essential provider of threat intelligence to allied governments.
- The technological modernisation frame positions defence spending increases and new weapons systems as necessary responses to emerging threats. This frame naturalises arms racing and technological competition, creates analytical demand for the products of IISS corporate funders (UAVs, space systems, cyber capabilities), and legitimises the defence-industrial base as a necessary component of security policy.
These frames are not random. They perform specific institutional functions: maintaining legitimacy, securing funding, and positioning the IISS as the natural convener of security dialogue within a particular geopolitical alignment. The constancy of the independence frame despite documented funding dependencies is the analytically significant finding: it suggests the frame serves a boundary-maintenance function essential to institutional operation.
The output pattern supports multiple functions simultaneously: producing genuinely useful reference data, maintaining IISS visibility in policy debates, generating content that supports funding applications, sustaining the elite networks necessary for dialogue convening, and seeding the analytical frameworks that shape how defence ministers understand the threats they gather to discuss.
The System Beneath: Feedback, Emergence, and Boundaries
The IISS operates as a system whose behaviour emerges from the interaction of its components. Multiple reinforcing feedback loops drive institutional growth and stability.
- A growth loop connects output volume to media visibility to funder interest to research capacity and back to output volume. As the Institute produces more analysis, more policymakers, journalists, and funders encounter it. Funders invest, enabling staff expansion, enabling more output. The loop has driven growth from one London office in 1958 to five global offices today, with income rising from £24.5 million to £32.3 million in just two years.
- A prestige loop connects elite network integration to dialogue attendance quality to dialogue prestige and back to network integration. The Shangri-La Dialogue attracted 553 delegates in 2022 and 581 in 2024, including 32 defence ministers each year. The Manama Dialogue grew from 300 delegates in 2021 to over 560 in 2023. Each year’s attendance reinforces the next year’s prestige. Ministers attend because other ministers attend. The loop is self-sustaining.
- A host-nation dependency loop connects Bahraini funding to the IISS-Middle East presence to the Manama Dialogue platform to Bahrain regime legitimacy benefits to renewal of Bahraini funding. The leaked 2016 MoU documented a five-year renewal; the pattern has repeated across multiple cycles. The Manama Dialogue has been held in Bahrain continuously since 2004, with the single exception of 2011.
- A personnel circulation loop connects government-to-IISS personnel movement to IISS access to government networks to IISS value to funders to IISS employment attractiveness to government officials—and back to personnel movement. The 65 percent revolving-door rate documented in the personnel architecture is both input to and output of this loop. Each former official hired strengthens the networks that make the Institute valuable to the governments those officials left. Each year of Dialogue attendance by sitting ministers strengthens the career case for future officials to move through the Institute.
- A balancing loop operates more quietly within the system. Analysis that would offend host nations or major funders creates risk. The risk incentivises self-censorship—whether through editorial judgment, topic avoidance, or softening of language. The self-censorship avoids triggering funder sensitivity. The funding is renewed. The institution survives. The analysis that would have been published is not. The pattern is not directed by any individual. It emerges from the aggregate effect of funding dependency, personnel career incentives, editorial norms, and the institutional imperative to maintain host-nation relationships.
From this system, emergent properties arise that cannot be reduced to individual decisions. The systematic omission of host-nation criticism is a property of the system as a whole, not of any single researcher or editor. No policy mandates it. No funder demands it in the text of an agreement. It emerges from the structure. Institutional credibility, similarly, emerges from multiple reinforcing mechanisms operating together: reference-quality data products, elite convening, media presence, prestigious personnel, and institutional longevity. No single element produces credibility; all are required.
The system’s boundaries are drawn tightly around funder interests.
- The mission boundary defines “security” in terms that exclude domestic repression in host nations and human rights as a security dimension. The IISS frames security as inter-state military capability, geopolitical risk, and strategic dialogue—concepts that align with Western government and military interests while excluding dimensions inconvenient for host-nation funders.
- The programmatic boundary operates distinctly from the mission boundary: research programmes are structured to attract government and corporate funding, meaning the research agenda is shaped by funding availability rather than comprehensive security analysis. Research on Bahraini military and police repression does not appear because no funder commissions it. Research on UK arms sales to authoritarian regimes and their security implications does not appear because it would complicate relationships with the UK government—the Institute’s home-state funder. Research on defence contractor influence on security policy does not appear because it would implicate IISS corporate funders. The exclusion is achieved through topic selection rather than content suppression, making it harder to detect and harder to challenge.
- The personnel boundary selects for individuals with government, military, intelligence, and elite academic backgrounds—systematically excluding critical scholars of the security establishment, human rights researchers, and individuals who have publicly criticised IISS host nations. Personnel homogeneity produces analytical homogeneity. Alternative perspectives are excluded from the institutional voice not through rejection but through the hiring process itself.
- The output boundary produces analysis that informs policy within existing institutional frameworks—excluding analysis that fundamentally challenges Western alliance architecture. IISS outputs operate within a bounded analytical space that reinforces the legitimacy of existing security institutions and policies.
Viewed across five dimensions, these boundaries are comprehensively aligned with Western security establishment interests—a structural signature of the institution’s ecosystem evolution. Spatially, analysis concentrates on Western-allied institutional ecosystems, excluding non-aligned and Global South security frameworks. Temporally, the post-1958 security order is treated as natural rather than historically contingent; longer patterns of colonialism and imperialism as security frameworks are invisible. Sectorally, defence and military security dominate, with limited coverage of human security, economic justice, climate security, or public health. In terms of actors, states, militaries, defence contractors, and elite think tanks constitute the universe of relevant players—social movements, human rights organisations, labour unions, diaspora communities, and indigenous groups are excluded. And in terms of knowledge, quantitative defence data, strategic analysis, geopolitical risk assessment, and elite interviews are privileged over ethnographic methods, participatory research, affected-community testimony, or historical-structural analysis.
This alignment is not maintained through explicit exclusion policies but through institutional inertia, funding incentives, personnel selection, and the taken-for-granted assumptions of the security establishment the IISS inhabits. The boundaries are not primarily enforced—they are inhabited.
The Ecosystem: Position, Pressures, and the System It Defends
Within the Western security governance ecosystem, the IISS occupies a distinct niche. It functions as a central coordination node connecting serving and former officials from multiple governments, defence contractors, foundations, and other think tanks. It facilitates connections that governments cannot officially arrange—track-1.5 dialogues where officials speak in personal capacity, private bilateral meetings at major conferences, informal exchanges between defence ministers who would otherwise not meet. This function creates network dependency on the IISS platform: governments need it because it can do what they cannot.
The Institute's position is not uncontested. RUSI and Chatham House compete on analytical output and London convening power. CSIS competes on Washington access and US policy influence. The Munich Security Conference and Halifax International Security Forum compete on the dialogue calendar. Government analytical capabilities compete with IISS open-source products. But the IISS has carved a unique niche: the Shangri-La Dialogue has no direct equivalent in the Asia-Pacific—no other forum brings together 32 defence ministers annually in that region. The Manama Dialogue occupies a similarly singular position in Middle East security convening, though one enabled by the very Bahraini funding dependency that constrains the Institute's Middle East analysis. This niche is defended by the funding dependencies that limit the Institute's independence, creating a paradox at the ecosystem level: the features that make the IISS valuable to stakeholders are the same features that constrain its analytical autonomy.
The Institute functions as a funding conduit: governments and corporations provide resources, the IISS produces analysis and convenes dialogues, funders receive analytical products, network access, and legitimacy, and the cycle renews. Critical dependencies include host-nation funding from Bahrain for the IISS-Middle East operation, host-nation support from Singapore for the Shangri-La Dialogue, UK government research grants, defence contractor corporate partnerships, and endowment income from Japan that provides partial buffer. The funding ecosystem is bounded by geopolitical alignment: resources flow from Western and allied governments, from corporations with interests in defence and security sectors, and from foundations whose priorities align with the IISS research agenda.
Within the policy ecosystem, the IISS functions as an agenda-setter: flagship publications establish baselines for security debate, dialogue agendas legitimise particular policy framings, and expert authority amplifies funder-aligned perspectives. The Institute does not contest the fundamental architecture of Western security institutions. It operates to make that architecture function more effectively.
Slow-moving pressures
Several long-term trends exert pressure on the IISS system over decades. The shifting centre of global economic gravity toward Asia is reflected in the Institute's Indo-Pacific programme expansion, the Japan Chair endowment, and the growing prominence of the Shangri-La Dialogue. Generational turnover in elite personnel gradually changes the networks the Institute can access. The erosion of US unipolarity creates tension between the IISS's embeddedness in Western alliance architecture and the multipolar reality its analysis must navigate.
These slow variables have shaped IISS programme priorities over decades. The Institute's founding in 1958 responded to a specific moment—post-war nuclear anxiety and the need for informed debate on deterrence. Its subsequent evolution traced the contours of Western security concerns: Cold War alliance management, post-Cold War regional conflicts, post-9/11 counterterrorism, post-2014 Russia confrontation, and post-2022 Ukraine war. Each shift realigned research programmes with funder priorities while the independence frame remained constant. The question slow variables pose is whether the IISS can adapt to a genuinely multipolar order without sacrificing the Western-aligned funding architecture that sustains it—or whether adaptation would require a different resource model entirely.
The system defended
The IISS does not defend a particular government or policy. It defends a broader architecture: the post-WWII system of US-led alliance systems, multilateral security institutions, the defence-industrial base, and the elite diplomatic processes that manage inter-state security relations within this framework. It defends this system not through advocacy but through function—by making the system work more effectively, by providing the analytical infrastructure and diplomatic facilitation it requires, and by excluding perspectives that would challenge its premises.
This system's documented characteristics include US military primacy, NATO as the central European security institution, bilateral US alliances in the Asia-Pacific, Gulf monarchies as Western security partners, the defence-industrial complex as a legitimate economic and strategic sector, elite diplomatic processes as the appropriate mechanism for security governance, state-centrism in security analysis, and technological superiority as a security strategy.
A test of analytical symmetry: if the IISS were a Chinese think tank hosted by an authoritarian state with documented torture, receiving one-third of its revenue from that state, deporting independent delegates at regime request, and staffed by officials moving directly from government to think-tank roles—the IISS's own analysts would classify it as a state-aligned institution performing legitimacy production, not an independent research body. The differential treatment of Western-allied versus adversary-aligned institutions is itself a finding about how security knowledge production functions.
What Is Not Said and Why It Cannot Be Said: Omissions and Contradictions
Three criteria define when an omission is analytically significant: the topic must lie within the institution's stated purpose, peer entities must address it, and the absence must persist over time.
The omission of Bahraini human rights from IISS Middle East analysis meets all three. The IISS mission includes providing “objective information on military and political developments” globally. Human rights organisations have extensively documented torture, political imprisonment, and discrimination against Bahrain's Shia majority. And the omission has persisted for over fifteen years—the entire duration of the Manama Dialogue and the IISS-Middle East office.
The omission of the IISS's own 2015 delegate deportations is equally persistent. In October 2015, Bahraini authorities revoked visas and removed five independent Yemeni researchers — including Farea al-Muslimi and Sama’a al-Hamdani—who had been invited by the IISS to attend the Manama Dialogue. The Institute facilitated their departure but has never publicly addressed the incident, issued an apology to the affected scholars, or explained why it continues to hold its primary Middle East security dialogue in a country that deports independent voices invited to its own event. This silence has now lasted nearly eleven years. The omission protects the host-nation relationship essential to institutional survival.
These omissions are not accidental gaps. They are structural features of an institution whose survival depends on maintaining alignment with funder interests. And they reveal contradictions the IISS must manage to function.
- The contradiction of knowledge – The Institute claims to provide “the best objective information” while systematically excluding information about Bahraini regime repression. It cannot simultaneously provide comprehensive objective information and maintain the Bahraini relationship.
- The contradiction of participation – The Manama Dialogue is described as “open and inclusive” while hosted in a country that deports independent voices. Nicholas Kristof has been denied a visa every year since 2011. Of 108 invited Bahraini delegates in 2015, only one was not pro-government.
- The contradiction of personnel – Sixty-five percent of senior leadership arrived directly from government service, yet the Institute claims independence. The same pattern in an adversary institution would be classified as state capture.
- A productive contradiction – The IISS produces genuinely useful reference data while simultaneously serving elite coordination functions. The two functions are mutually reinforcing: credible data attracts elites; elite participation validates the data's importance.
The Institute manages these contradictions through self-presentation—framing the revolving door as expertise rather than alignment—through silence about documented harms, and through organisational design separating reference products from policy-serving analysis. The contradictions are not problems to be solved. They are the mechanism through which the institution maintains productive ambiguity between its independence claims and its structural dependencies. The omissions are not failures of coverage. They are the visible traces of these contradictions in the output record.
The De Facto Purposes: What the Institution Actually Does
The IISS, assessed through what it does rather than what it says, reveals a layered functional architecture. Its stated purpose—providing independent, objective analysis to inform security policy and facilitate conflict resolution—is partially realised through genuinely valuable products. The evidence is clear: The Military Balance provides reference-quality open-source defence data that governments, researchers, and journalists across the political spectrum rely on. The Shangri-La Dialogue enables diplomatic exchanges between defence ministers who might otherwise not meet, including representatives of competing powers.
The observable outcome is an institution that simultaneously serves multiple functions: producing useful analytical products, facilitating elite coordination, generating legitimacy for host-nation funders, and maintaining its own institutional growth. The resultant state is an organisation whose various functions exist in productive tension, none fully dominating, all necessary for institutional survival.
At the internal level, the de facto purpose—visible in resource allocation, personnel selection, and institutional priorities—is elite network maintenance and institutional growth within the Western security establishment ecosystem. Independence claims and analytical products serve as means to that end. The evidence suggests this with moderate confidence: the personnel architecture, funding structure, and output synchronisation patterns are documented; intentionality about the hierarchy of purposes is not.
At the ecosystem level, the de facto purpose is enabling coordination and legitimacy production that governments and corporations cannot perform directly, while maintaining the appearance of independence that makes those functions valuable.
The competition index reveals a dual-dominant pattern: elite coordination and legitimacy production are co-dominant functions, with remaining functions operating as supporting mechanisms. The Institute’s primary cybernetic function is homeostatic regulation: maintaining the stability and legitimacy of the Western-allied international security order through elite coordination, agenda-setting, signal amplification, and boundary maintenance.
Secondary functions support this primary function. Agenda-seeding places IISS analytical frameworks into policy debate before ministerial discussions—the Strategic Dossier on unmanned aerial vehicles published 65 days before the Shangri-La Dialogue, the civil defence paper launched simultaneously with the Stockholm Forum. Signal amplification sustains funder-aligned perspectives through continuous output: same-day analysis of Japanese defence export liberalisation, consistent framing of technological modernisation as necessary, sustained focus on Russia and China as primary threats. Legitimacy production serves host-nation funders, particularly Bahrain, through platform provision and systematic information exclusion—the Manama Dialogue presenting the regime as a responsible security partner while excluding documentation of torture and political imprisonment. Revenue generation through Military Balance+ subscriptions, IISS Advisory services, and Six Analytic consultancy provides the commercial income stream that supplements government and corporate funding.
An alternative interpretation warrants acknowledgment: this being that the IISS functions as an independent platform that governments choose to engage because it provides genuinely useful analysis and neutral convening space. Under this liberal institutionalist framework, the Institute’s funding diversity—100-plus separate funders across multiple categories—its formal independence policies, and its genuinely diverse dialogue participation demonstrate institutional autonomy. The IISS includes both US and Chinese defence ministers at the same forum; its analysis is produced by researchers with academic freedom; governments attend voluntarily.
The evidence favours the primary interpretation because the alternative cannot adequately explain patterns that the primary interpretation predicts: the systematic omission of host-nation criticism persisting across fifteen-plus years and all output types, the documented delegate deportations without institutional protest or policy change, and the structural alignment between funding sources, personnel backgrounds, and output framing. Under the alternative framework, these patterns require special explanation as exceptions. Under the primary framework, they appear as predictable features of the institution’s ecosystem position—not deviations from independence but boundary conditions that define where independence ends.
The Stakes: Who Benefits, Who Pays
The system described above distributes benefits and costs unevenly across populations. These are not abstractions. They are the material consequences of institutional design.
Who benefits:
- Western and allied governments receive analytical validation for strategic priorities and a platform for unofficial diplomatic coordination—track-1.5 dialogues and private bilateral meetings that formal state channels cannot easily arrange.
- Defence contractors gain intellectual frameworks that naturalise technological modernisation as necessary response to emerging threats, creating analytical demand for their products.
- Host nations, particularly Bahrain, receive an annual platform that presents them as responsible security partners to an international audience while the Institute systematically excludes documentation of the repression that characterises their rule.
- IISS personnel gain career advancement, elite network access, and credentials that facilitate movement between government, corporate, and academic roles.
Who pays:
- The costs fall on populations already subjected to state violence. Bahraini democracy activists, political prisoners, and torture survivors see the regime that imprisoned them legitimised annually by one of the world's most prestigious security institutions. The Shia majority of Bahrain—approximately sixty percent of the population—are structurally excluded from the dialogue that claims to represent regional security. Of 108 invited Bahraini delegates to the 2015 Manama Dialogue, only one was not pro-government and only a handful were Shia.
- Independent scholars and journalists who attempt to bring critical perspectives are deported or denied entry. Yemeni scholars invited to the 2015 Dialogue were removed at regime request, the IISS staff facilitating their departure. Nicholas Kristof of the New York Times has been denied a visa every year since 2011. Palestinian civil society voices appear only at the margins of IISS coverage of the Gaza war, which operates within a strategic-military framework that does not centre affected-population perspectives. Non-Western security scholars outside the alliance framework, Yemeni civil society, and independent researchers excluded from dialogue venues all experience the boundary as a wall.
- Populations affected by the security policies the IISS analyses—civilians in conflict zones, communities subject to arms proliferation, people living under authoritarian regimes supported by Western security partnerships—have no voice in the Institute's governance, funding, or research agenda. Their perspectives are systematically excluded from the analysis that shapes elite security discourse.
Accountability is structurally weak
The IISS is accountable to its Board of Trustees—self-perpetuating and drawn from the elite networks the institution serves. It is accountable to its funders, whose interests shape its resource environment. It is accountable to the UK Charity Commission for financial and governance compliance. It is not accountable to the populations whose security it claims to address, the scholars it invites and then facilitates the removal of, or the publics that consume its analysis without visibility into the dependencies that shape it.
The populations whose security the IISS claims to serve include, in Bahrain, the same populations whose repression the IISS enables by legitimising the regime that represses them. The exclusion of independent voices from the Manama Dialogue is not an anomaly. It is the predictable output of a system whose survival depends on maintaining host-nation relationships. The Institute's silence about its own contradictions is not neutral. It is a choice with consequences that fall differentially on populations already subjected to state violence.
Conclusion
The IISS embodies a core paradox of Western security governance: it is genuinely independent in its analytical methods while remaining structurally aligned with the governments, defence contractors, and authoritarian host nations that sustain it. This is not hypocrisy or corruption in the conventional sense. It is an emergent property of the system the Institute inhabits—a sophisticated legitimacy engine that provides analytical infrastructure, elite coordination, and reputational cover that its stakeholders cannot easily generate themselves.
Some patterns revealed here are sector-wide: heavy government and corporate funding, revolving-door personnel flows, and research agendas shaped by funder priorities characterise most major Western security think tanks. Others are more specific to the IISS: the unusually deep financial and hosting relationship with Bahrain, the documented 2015 delegate deportations without public institutional response, and the fifteen-year systematic omission of Bahraini human rights documentation from its Middle East analysis.
The tension is not incidental. The IISS produces genuinely valuable reference material, most notably The Military Balance. At the same time, it systematically excludes documentation of repression by a regime that has long been one of its major funders. Both statements are true. That productive contradiction — usefulness paired with selective silence—defines the institution more accurately than either its independence claims or its critics’ strongest accusations.
Whether this model is sustainable remains open. The erosion of unipolarity, shifting global economic gravity, and growing domestic scrutiny of elite institutions create long-term pressures. Possible paths forward range from modest reforms (rotating dialogue venues, greater transparency on host-nation agreements) to more fundamental changes (structural separation of analytical and convening functions, or a genuine broadening of whose security is considered).
The deeper question is whether an institution so deeply embedded in the existing architecture can meaningfully contribute to rethinking that architecture. The evidence suggests its primary cybernetic function is homeostatic: maintaining and legitimising the current system rather than challenging its foundations.
Readers of IISS analysis should therefore approach its outputs with informed realism. The Institute offers real expertise and convening power. It also operates within clear structural boundaries. Understanding both is essential to reading its work responsibly.
Published via Mindwars Ghosted.
Geopolitika: Tracing the architecture of power before it becomes the spectacle of history.
Methodology Note: This analysis examines the IISS through its own documents, personnel records, funding disclosures (Charity Commission and Companies House filings), output patterns, and publicly available investigations. Institutional self-presentation is treated as interested communication requiring independent corroboration. Counter-sources were assessed at parity with official materials. The analysis was conducted using a structured institutional analysis framework examining self-presentation, personnel networks, funding architecture, output patterns, synchronisation, contradictions, missing materials, and de facto purpose. All sourced material is publicly accessible. Base analytic outputs are available on request. For methodological details—including Transparency Score definitions, typology classifications, and confidence calibration—see the Geopolitika Series Methodological Statement.
Mindwars Ghosted is an independent platform dedicated to exposing elite coordination and narrative engineering behind modern society. The site has free access and is committed to uncompromising free speech, offering deep dives into the mechanisms of control. Contributions are welcome to help cover the costs of maintaining this unconstrained space for truth and open debate.
If you like and value this work, please Buy Me a Coffee.